Igleak Info App Full Pack All Files Instant
Watch For Free igleak info app unrivaled watching. Free from subscriptions on our digital collection. Engage with in a endless array of curated content presented in HDR quality, tailor-made for premium viewing patrons. With newly added videos, you’ll always stay updated. Browse igleak info app arranged streaming in vibrant resolution for a totally unforgettable journey. Sign up for our streaming center today to get access to private first-class media with at no cost, no commitment. Get fresh content often and journey through a landscape of singular artist creations developed for first-class media lovers. Make sure to get special videos—begin instant download! Enjoy the finest of igleak info app exclusive user-generated videos with stunning clarity and members-only picks.
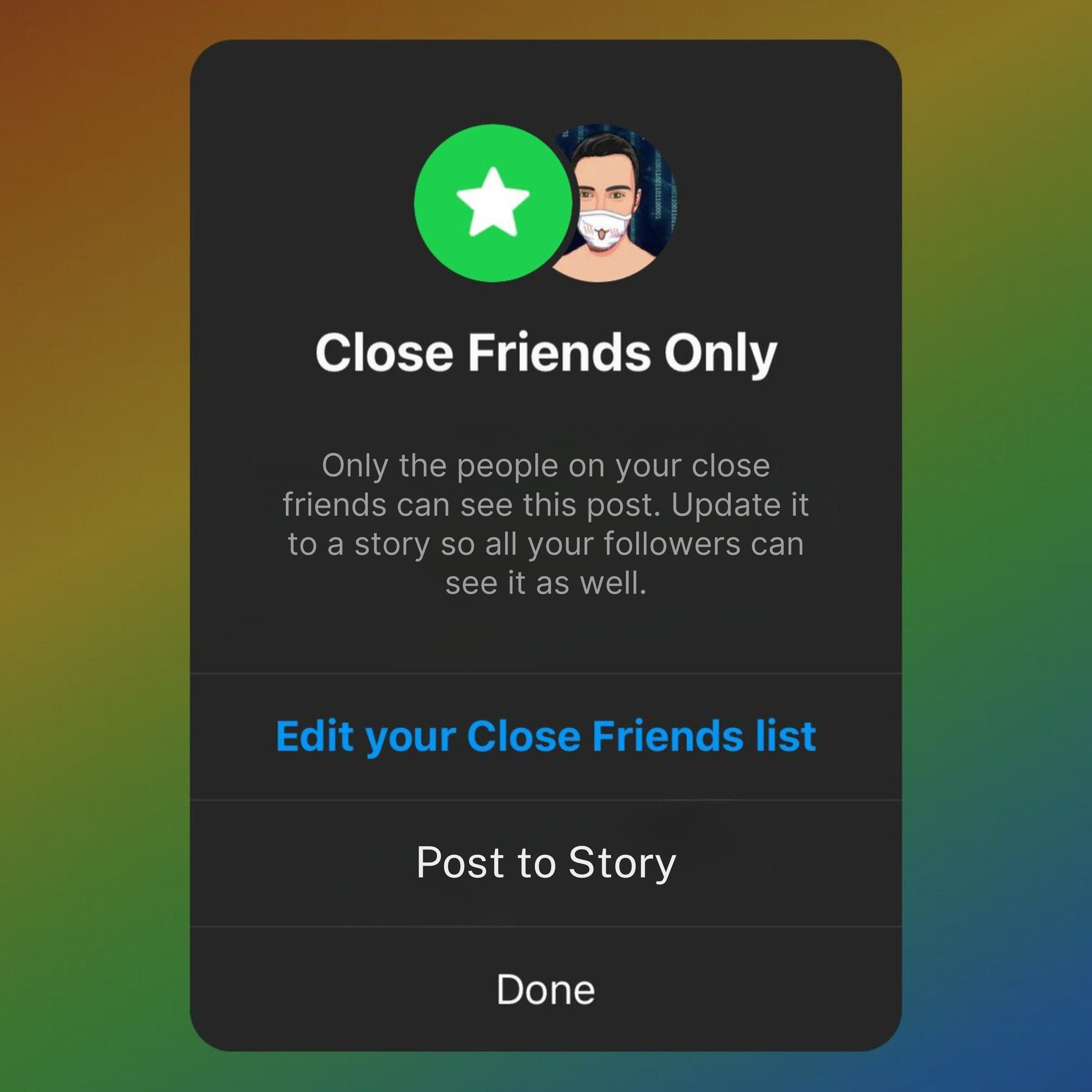
Check igleak.info with our free review tool and find out if igleak.info is legit and reliable Telephone number, date of birth or address), has been made. Instagram generatormobile device requiredinstagram generator
App info - Android App Source Code by CodeMaxInfotech | Codester
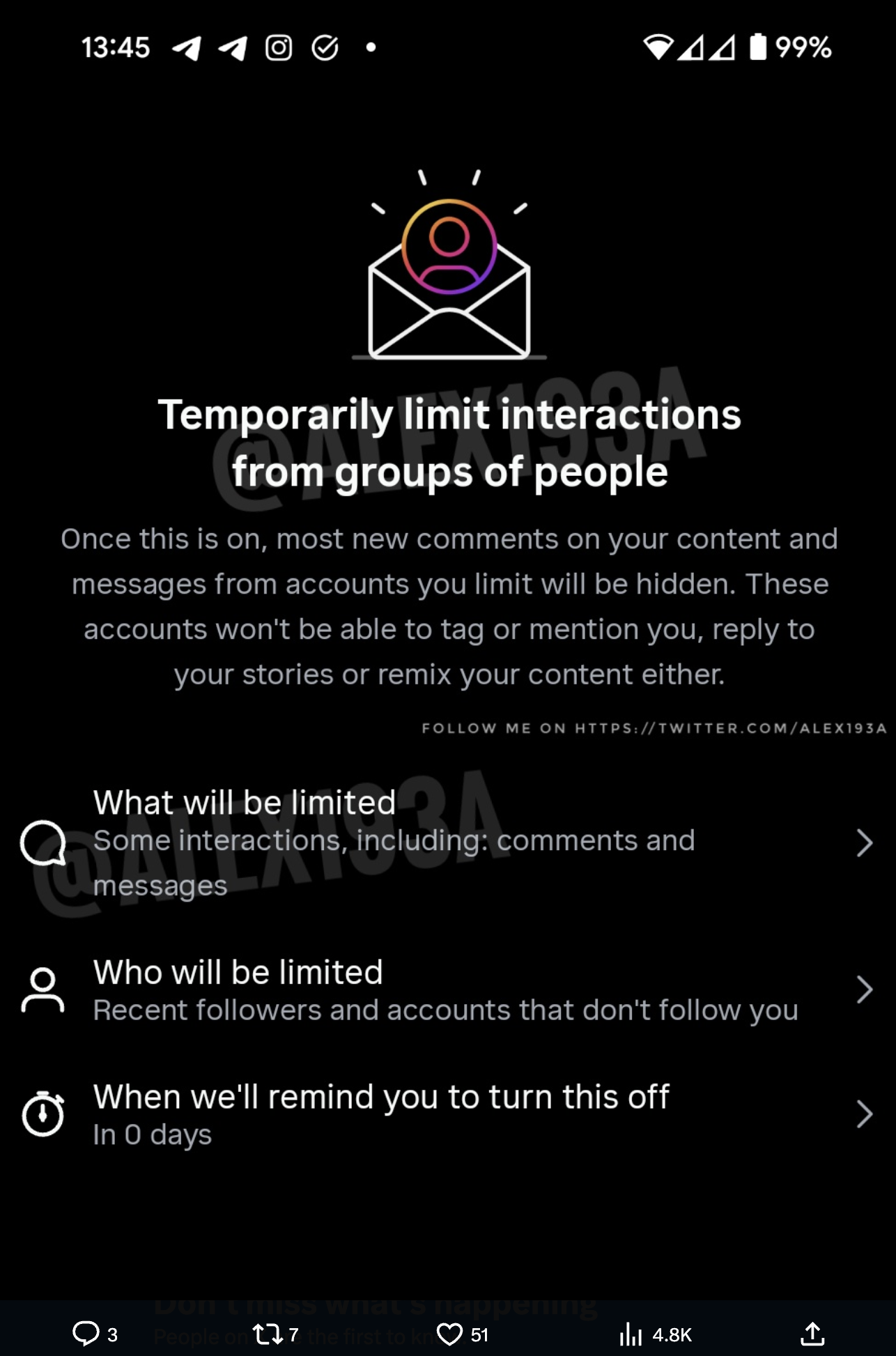
Important distinction when discussing this as saying hacks can give the idea that someone is accessing your dm's through apps or code, when the reality of this is that it's a common scam tricking you to give away your password or login info. With the hpi identity leak checker, it is possible to check whether your email address, along with other personal data (e.g The personal details of up to six million instagram users have reportedly been leaked online after a bug in the platform made profiles' account information publicly accessible.
Trustedsite offers an earned certification program for online businesses to help shoppers identify secure sites that demonstrate good business practices.
Includes tasks such as fraud prevention, literature reviews, content, websites and email marketing. A digital privacy and security concern igleak.info app has, of late, been in the news in the digital world According to its claims, it provides access. A large part of the stolen information is subsequently made public on internet databases, where it serves as the starting point for other illegal activities