Leaks Application Full Library Vids & Pics Access
Claim Your Access leaks application VIP webcast. No wallet needed on our content platform. Submerge yourself in a huge library of expertly chosen media provided in superb video, a dream come true for select watching patrons. With the freshest picks, you’ll always get the latest. Discover leaks application curated streaming in photorealistic detail for a truly engrossing experience. Join our video library today to feast your eyes on special deluxe content with cost-free, no need to subscribe. Stay tuned for new releases and navigate a world of bespoke user media engineered for top-tier media lovers. Be sure not to miss specialist clips—rapidly download now! Experience the best of leaks application singular artist creations with lifelike detail and unique suggestions.
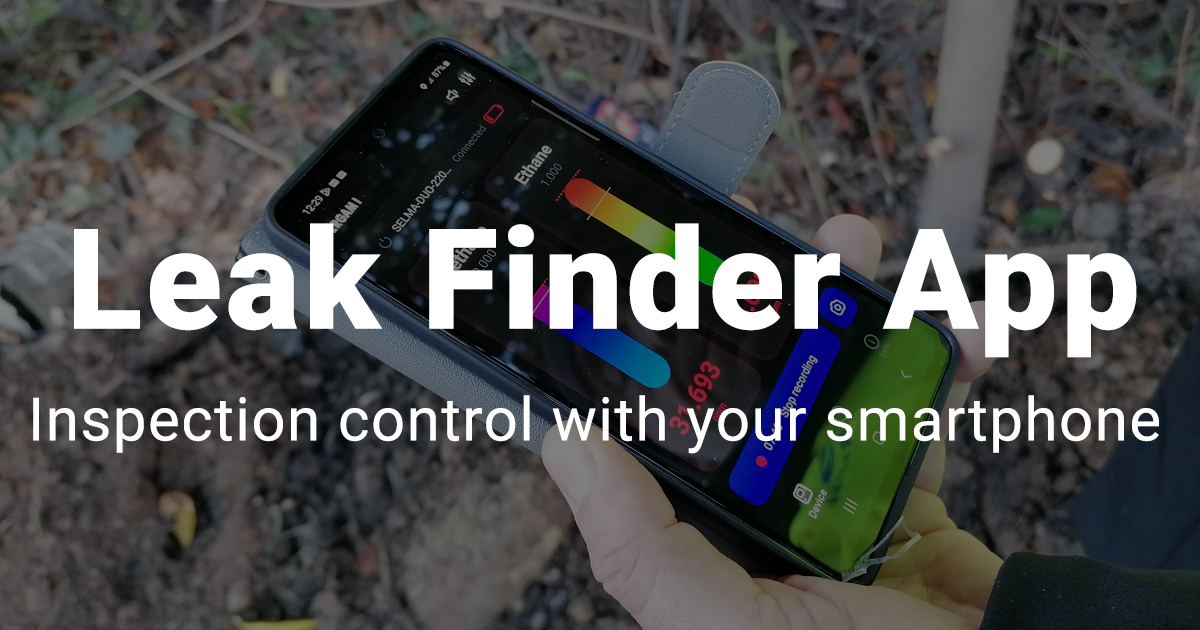
Most of the time you won't know until it's too late The app and the sensors work together to find leaks, and then when they are sure of the location of a leak, they use both audio and visual alerts on the sensors and your phone to inform you What exactly is happening when an app leaks data
Architecting Software Observability in .NET Core | by Patrick | Nov
App leaks involve the unauthorized or unintentional transfer of sensitive information from a mobile device to an internet service One such revolution has occurred in the domain of leak detection, thanks to the development of mobile applications. It is often the result of security measures being deprioritized in the app development process.
Leaky apps, which unintentionally expose sensitive data, pose a growing risk to mobile security
These apps can leak critical information like your location and contacts, creating vulnerabilities across mobile ecosystems In this blog, we dive into the hidden dangers of leaky apps and how quokka's mobile security intelligence helps organizations detect and mitigate these threats Leak relief program the water leak relief pilot (lrp) program is a new pilot program that seeks to provide debt relief to eligible customers who experience water leaks that cause unexpected increases in their bills I have an application that uses zxing barcode scanner library, but when i run the application on the device, there is another additional application installed called leaks
Why is this application installed on the device When i open it nothing happens ? This guide outlines the main considerations of effective data leak detection software and the best solutions currently on the market. Hackers are certainly not above using news about data leaks as an occasion for reaching out to defraud users
For any communications you receive about data, passwords, accounts, or any transactions you've made (or pines you haven't!) — always double check the source.
Learn about the hidden data risks in mobile apps, focusing on cloud and cryptography vulnerabilities that could expose sensitive information Discover how to protect your enterprise. Worried about data leaks from apps Learn how leaky apps compromise your data and discover steps to prevent unauthorized access.
Leak detection application for generating reports in today's era of technological advancements, the way we address and handle issues in various industries has transformed remarkably
![How to Find Memory Leaks in Web Applications [Example] - Sematext](https://sematext.com/wp-content/uploads/2021/02/How-to-Find-Memory-Leaks-in-Websites-and-Web-Applications.png)