Honeypot Leak Full Files Vids & Images Instant
Enter Now honeypot leak hand-selected playback. No monthly payments on our digital collection. Become absorbed in in a wide array of documentaries showcased in Ultra-HD, tailor-made for first-class watching viewers. With fresh content, you’ll always stay in the loop. Encounter honeypot leak arranged streaming in incredible detail for a truly captivating experience. Register for our creator circle today to experience VIP high-quality content with absolutely no charges, no subscription required. Experience new uploads regularly and navigate a world of groundbreaking original content optimized for elite media enthusiasts. Make sure to get original media—get it fast! Enjoy the finest of honeypot leak singular artist creations with impeccable sharpness and selections.
Discover how crypto honeypot scams work, why they're dangerous, and how to avoid falling victim to one They can see what vulnerabilities hackers target and how they break in, then use that. Stay safe in defi and web3.
honey.pots / thehoneypotco Nude, OnlyFans Leaks, Fappening - FappeningBook
Over the course of a year, vpnmentor deployed a honeypot of open servers containing fake personal data to lure outside actors, analyze their behavior, and record what happens once It's designed to be attacked so cybersecurity experts can study hackers and improve defenses.honeypots allow cybersecurity teams to get valuable intel about hacker behavior without putting real systems and data at risk Honeypot1766 leaks expose sensitive data, including personal information and potentially financial records
This article details the breach, its impact, cybersecurity vulnerabilities, data privacy concerns, and offers advice on protecting yourself from similar online security incidents
Learn more about the fallout. Hackers also use honeypots on other hackers, hoping adversaries will accidentally leak data that identifies them Law enforcement uses honeypots to catch criminals. Scan a token to check it's honeypot status, fees, gas usage and more
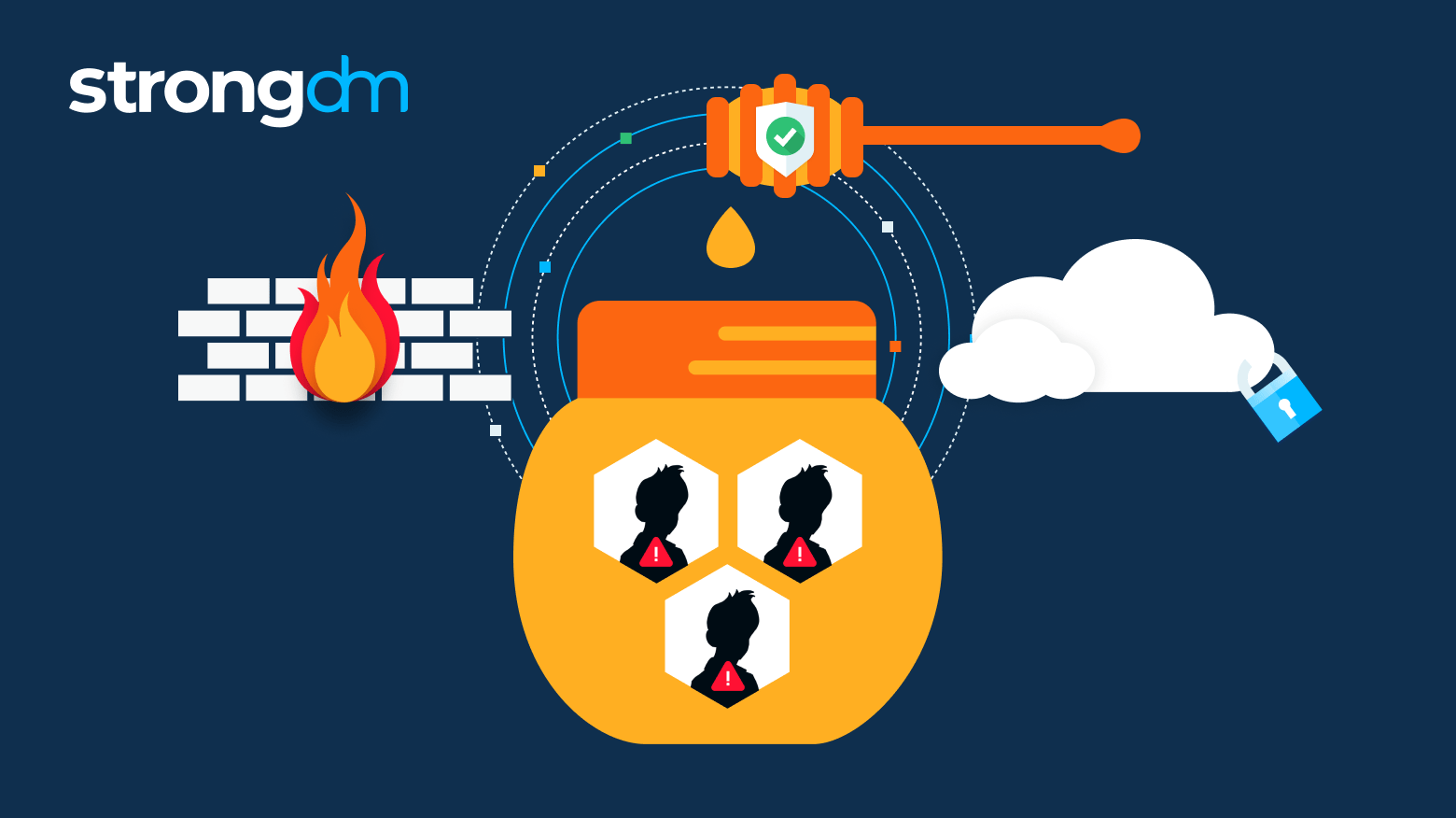
Crypto's most advanced honeypot detection. A honeypot is a trap set to detect hackers Reentrancy attack is one of the vulnerabilities that affects decentralised systems badly To combat such threats, developers employ techniques like.

Learn how honeypot traps are used to improve cybersecurity and discover whether it's illegal to set honeypots.
Llm honeypots fooled actors into revealing payloads by mimicking real servers via natural ai chats, capturing exploits and backdoor attempts. What is a honeypot in cybersecurity A honeypot is a computer system set up as bait